Information Security: What’s Private?
Printed Page 280
Government surveillance, online fraud, and unethical data-gathering methods have become common, making the Internet a potentially treacherous place.
- Government Surveillance. Since the inception of the Internet, government agencies around the world have obtained communication logs, Web-browser histories, and the online records of users who thought their Internet activities were private. In a traditional wiretap, a police agency gets court permission to listen in on a single telephone line. When investigating Internet communications, an agency captures the communications of every user of an Internet service provider. While agencies use this information to target criminals and terrorists, the scope of Internet surveillance procedures raises questions about just how far into our private lives the government should be allowed to reach.
- Online Fraud. The Internet has increasingly become a conduit for online robbery and identity theft, the illegal obtaining of someone’s credit and identity information to fraudulently spend his or her money. One particularly costly form of Internet identity theft is phishing. Through this tactic, scammers send phony e-mail messages that appear to be from official Web sites—e.g., eBay, PayPal, AOL—asking customers to update their credit card details and other personal information (such as bank account numbers). Once scammers have this information, they can go on a shopping spree using the victim’s credit card or siphon funds out of the victim’s bank account.
- Unethical Data Gathering. Millions of people, despite knowing that shopping online can make them vulnerable to online fraud, have embraced the convenience of e-commerce: the buying and selling of products and services on the Internet. What many people don’t know is that a company may use their personal information without their knowledge for commercial purposes, such as developing targeted advertisements. One way companies do this is through cookies, information profiles that are automatically collected and transferred between computer servers whenever users access Web sites. Companies doing business on the Net use cookies to tailor their marketing messages to niche groups of users, which many people view as intrusive and even unethical. Even more frustrating is spyware, information-gathering software that’s often secretly bundled with free downloaded software and that sends pop-up ads to users’ computer screens. Spyware has also made it possible for unauthorized parties (such as hackers) to collect personal or account information about users and to plant viruses and malicious click-fraud programs on computers.
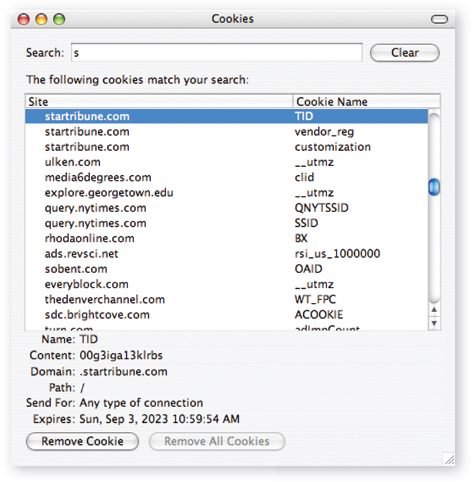
Several cookies from visiting the Minneapolis Star Tribune’s Web site will reside on this user’s computer until 2023, tracking every subsequent visit to the newspaper Web site unless the user manually removes the cookies.
In 1998, the U.S. Federal Trade Commission (FTC) developed fair-information principles to combat the unauthorized collection of personal data online. Unfortunately, the FTC has no power to enforce these principles, and most Web sites either don’t self-enforce them or say they do when they really don’t.4 Consumer and privacy advocates are calling for stronger regulations, such as requiring Web sites to adopt opt-in policies. Opt-in policies require a Web site to obtain explicit permission from consumers before it can collect their browsing-history data.